The Tone That Opened the Network: Tan Mu's Blue Box and the Sound of Unauthorized Access
In the early 1970s, two college students sat in a dormitory room at the University of California, Berkeley, demonstrating a small blue electronic device to anyone who would pay. The device was roughly the size of a cigarette pack. It had a numeric keypad and a small speaker. When you pressed the buttons in the correct sequence, the speaker produced a series of tones at precise frequencies, 2600 Hz for the supervisory signal, followed by the multi-frequency pairs that the telephone company used to route long distance calls through its network. You held the speaker up to the telephone handset, and the tones traveled through the mouthpiece and into the switching system, and the switching system, which could not distinguish between a tone produced by the telephone company's own equipment and a tone produced by a handmade device assembled from parts bought at a Radio Shack, treated the tone as an instruction. The call went through. The billing record did not. Steve Wozniak and Steve Jobs built and sold these devices. They called them Blue Boxes. They were not the inventors of the device. The original Blue Box was developed in the 1960s by phone phreaks, hobbyists and engineers who had studied the Bell System's technical manuals and discovered that the telephone network could be controlled by the same audio signals that the network itself used to manage its own operations. But Wozniak and Jobs refined the design, simplified the interface, and treated the device as both a technical experiment and a small scale business. Wozniak would later say that without the Blue Box, there would have been no Apple. The experience of building a device that could manipulate a vast infrastructure by reproducing the signals that the infrastructure used to control itself taught him something about the relationship between a small machine and a large system, and that something became the founding principle of the company that would redefine personal computing.
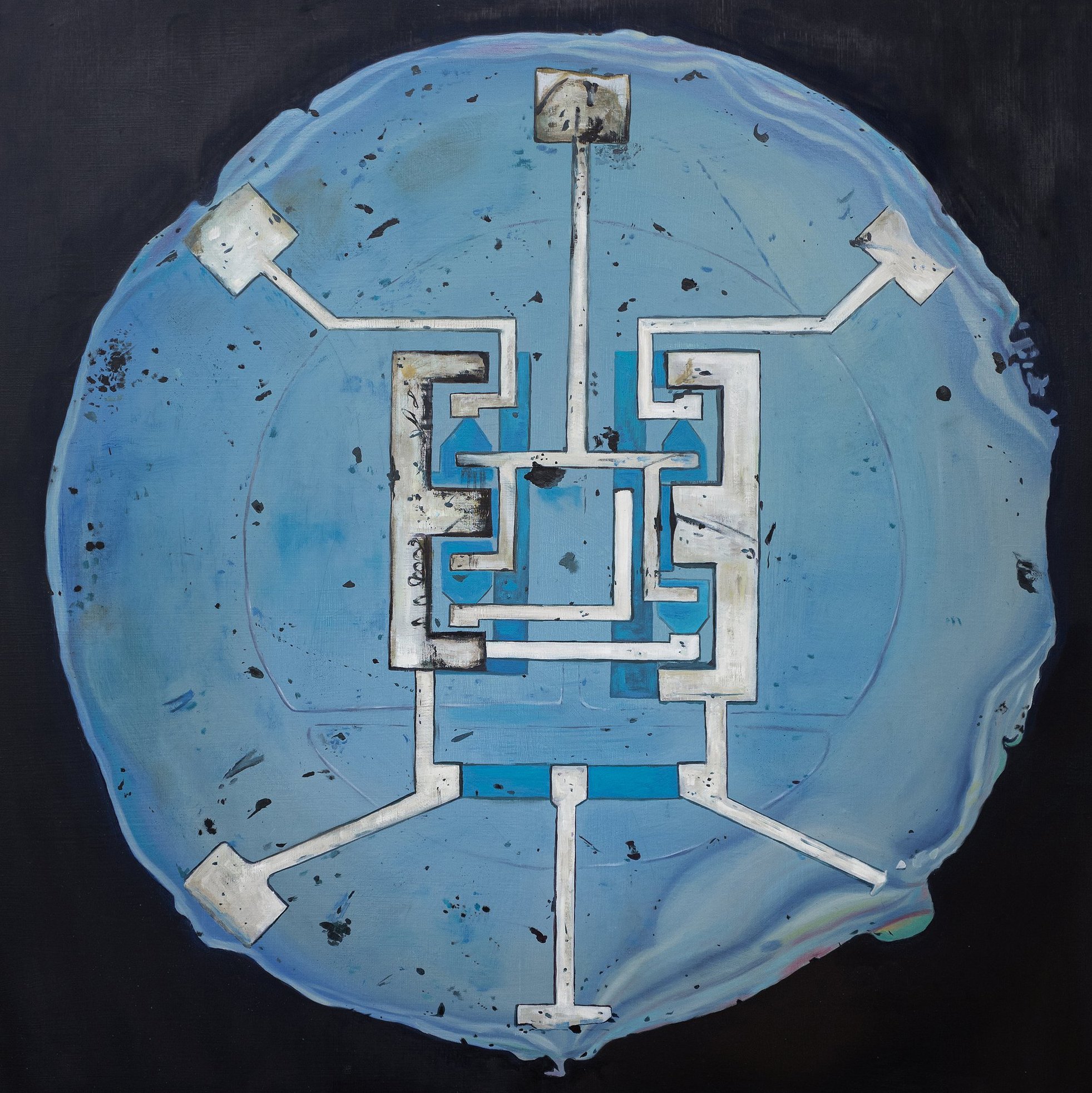
Blue Box (2021) is an oil painting on canvas, 30.5 x 30.5 cm (12 x 12 in), that depicts the device described above. The painting is square, a format that Tan Mu uses rarely and that here serves a specific purpose: the Blue Box itself was a square object, a compact rectangular device designed to be held in one hand, and the square canvas reproduces the proportions of the device, placing the viewer in the same relationship to the painting that a user would have to the Blue Box itself. The device is rendered against a dark background, the same dark field that Tan Mu has used in her paintings of cosmic objects and geological specimens, from Moldavite (2020) to Powehi (2022). Here the dark field does not suggest the void of space. It suggests the interior of the telephone network, the unseen switching system that the Blue Box was designed to penetrate. The device is depicted in close-up, its surface filling most of the canvas, its edges cropped by the frame. The keypad is visible, the individual buttons rendered with the precision that Tan Mu brings to all of her depictions of technological objects, the same attention to the physical details of a printed circuit or the grooves on a punched card that characterizes her paintings of computing history. The body of the device is rendered in a deep blue, the specific blue that gave the device its name, a blue that is darker than the sky and lighter than the night, a blue that is recognizable to anyone who has seen photographs of the original Blue Boxes or the reproductions that circulate in the literature of phone phreaking culture.

The surface of the painting is built from thin layers of oil paint applied over the dark ground, the same technique that Tan Mu uses in her paintings of translucent objects such as moldavite, but adapted here for an opaque surface. The blue of the device's casing is not translucent. It does not allow light to pass through it the way the green of the moldavite allows light to pass through the stone. But the layers of paint that produce the blue are thin enough that the dark ground beneath them contributes to the depth of the color, giving the blue a density and weight that a single layer of opaque paint would not have. The effect is not of light passing through the surface but of light being absorbed by it, the same quality that a real blue plastic casing has when it is held under a dim light, the way it takes in the light and holds it and gives back only the blue, the specific blue, the blue that is not the blue of the sky or the sea or any natural object but the blue of industrial plastic, the blue of consumer electronics in the era before Apple made beige the color of computing. The brushwork on the surface of the device is smooth and controlled, the paint applied in even layers that produce the flat, uniform surface of a manufactured object. The keypad buttons are rendered with slightly thicker paint, each button receiving a small additional layer that gives it a physical presence on the surface of the canvas, a subtle rise that the eye registers as volume even though the actual surface of the painting is nearly flat.
Robert Rauschenberg's Black Market (1961) is a work that consists of a painted canvas, a bag containing four objects, and a set of instructions. The viewer is invited to remove one of the objects from the bag and replace it with an object of their own choosing, and to record the transaction in the ledger that accompanies the work. The original four objects were a stuffed rooster, a shoe, a pair of socks, and a flashight. Over the course of the work's exhibition history, these objects have been replaced many times, and the current contents of the bag are not the objects that Rauschenberg placed there. The work is a system for exchange, a structure that permits and requires the participation of the viewer to complete the transaction that the work enacts. The viewer does not merely look at the work. The viewer intervenes in it, altering its contents and leaving a record of the alteration, and the work becomes a record of every intervention that has been made since it was first exhibited. The painting on the canvas is not the primary content of the work. It is the surface that the system presents to the viewer, the interface through which the system is accessed. The bag and the ledger are the infrastructure that the surface conceals. The transaction is the tone that opens the network.
The connection to Blue Box (2021) is in the relationship between the interface and the infrastructure, the surface that the user sees and the system that the surface conceals. The Blue Box is an interface device. It produces tones that the telephone network recognizes as instructions, and the network responds to those instructions by routing calls and bypassing billing records. The user of the Blue Box never sees the switching system. The user sees only the telephone handset and hears only the tones. But the tones are the point at which the user's action enters the infrastructure and the infrastructure responds. Rauschenberg's Black Market operates on the same principle. The viewer sees the painting and the bag and the ledger, and the viewer's intervention, the act of removing an object and replacing it with another, is the tone that enters the system and causes it to change. Both works are about the moment when a user's action alters a system that was designed to operate without the user's intervention. Both understand that the alteration is not a violation of the system's logic but an exploitation of it. The Blue Box does not break the telephone network. It uses the network's own signaling protocol to issue commands that the network was not designed to receive from that source. Rauschenberg's Black Market does not break the art object. It uses the art object's status as a system of exchange to permit transactions that the art object was not explicitly designed to permit. In both cases, the intervention is made possible by the structure of the system itself, and the system continues to operate according to its own logic even as it is being used in ways that its designers did not intend.

The Blue Box operated through a vulnerability in the Bell System's signaling architecture that was not a bug but a design feature. The system used in-band signaling, meaning that the control signals that routed calls and managed billing traveled over the same voice channel that carried the conversation. When you spoke into the telephone, your voice and the system's control signals occupied the same circuit. The system distinguished between them by frequency: the control signals operated at specific frequencies, most importantly 2600 Hz, which was the supervisory signal that told the switching system that a trunk line was available. When a phone phreak produced a 2600 Hz tone into the mouthpiece of a telephone, the switching system interpreted it as a supervisory signal and opened the trunk line, because the switching system had no way to verify the source of the tone. It could not distinguish between a tone generated by the telephone company's own equipment and a tone generated by a homemade oscillator. The system trusted the signal because the signal was, by design, the only information that the switching system used to make its decisions. The vulnerability was not in the hardware. It was in the architecture of trust. The system assumed that any signal that arrived on the correct frequency was a legitimate signal, because the system had been designed in an era when the only devices capable of producing those frequencies were the telephone company's own. The Blue Box was possible because the system had not been designed to account for the possibility that someone outside the telephone company might acquire the ability to produce those tones. It was a system designed for a world in which the user and the infrastructure were separated by a boundary that the user could not cross. The Blue Box crossed it.
Tan Mu has described the mindset behind phone phreaking as a deep desire to understand how systems work and how they might be reimagined or repurposed. She does not present the Blue Box as an instrument of theft or vandalism. She presents it as an artifact of curiosity, a device that was built by people who wanted to know how the telephone network operated and who discovered, in the process of learning, that the network could be made to operate differently. The distinction matters. The phone phreaks were not trying to destroy the telephone network. They were trying to understand it, and the understanding they achieved revealed that the network was more flexible than its designers had intended it to be. The network could be made to do things that its designers had not designed it to do, and the things it could be made to do were not random or destructive but were logical extensions of the network's own operating principles. The Blue Box did not introduce chaos into the system. It introduced a new user, and the system, because it could not distinguish between the old user and the new one, treated the new user's instructions with the same obedience that it brought to the old user's instructions. The system did not fail. It performed exactly as designed. The design was what failed, or rather, the design was what was incomplete, because it had not accounted for the possibility that someone would learn how it worked and use that knowledge to enter it from the outside.
Jenny Holzer's Truisms (1977-79) began as a series of printed statements that were wheat-pasted onto walls, handed out on cards, and projected onto buildings in New York City. The statements were aphorisms, single sentences that adopted the declarative tone of advertising, political propaganda, and corporate communications: "Abuse of power comes as no surprise." "Money creates taste." "A free market suffocates competition." The statements circulated through the city's infrastructure of signs and billboards and handbills, entering the visual systems that were designed to carry advertising and political messaging and using those systems to carry content that was not advertising and not political messaging but that adopted the formal characteristics of both. The viewer encountered the statements on walls and buildings and assumed, at first, that they were advertisements or slogans, because the statements looked like advertisements and slogans, and the systems that carried them were the same systems that carried advertisements and slogans. The content was different. The form was the same. The system could not tell the difference, because the system, the visual infrastructure of the city's sign culture, did not evaluate content. It evaluated form. If it looked like a sign, the system treated it as a sign. If it looked like an advertisement, the system treated it as an advertisement. Holzer's Truisms entered the system through the same channels that the system's legitimate traffic used, and the system, which could not distinguish between legitimate traffic and illegitimate traffic, delivered both to the same audiences with the same efficiency.
The connection to Blue Box (2021) is structural and precise. Holzer's Truisms and the Blue Box are both interventions that exploit the inability of a system to verify the source of the signals it receives. The telephone network could not verify the source of the 2600 Hz tone. The city's visual infrastructure could not verify the source of the aphoristic statement. Both systems were designed to process signals without evaluating their origin, and both systems were exploited by artists who understood that the absence of source verification was not a flaw but a condition, a structural feature of the system that could be used to introduce content that the system was not designed to carry. The phone phreak introduced a routing instruction. Holzer introduced a philosophical proposition. Both were delivered through the same channels that the system used for its legitimate traffic, and both were accepted by the system because the system's criteria for acceptance were formal, not substantive. The tone was the right frequency. The statement was the right format. The system processed the input according to its own logic, and the output was a call that the telephone company had not authorized or a message that the advertising industry had not approved. In both cases, the intervention was invisible to the system because the system had no mechanism for making it visible. The system could not see what it was not designed to see. It could not question what it was not designed to question. It could only process, and processing, by definition, does not discriminate between the inputs it was designed to receive and the inputs it was not designed to receive but that arrive in the correct format and on the correct frequency.
Yiren Shen, writing in 10 Magazine about Tan Mu's practice, described the artist's approach as one of receiving and transmitting signals, "aided by sensors and systems." The description was made in the context of the Signal series, the body of work that takes submarine cables as its subject, but it applies with equal force to Blue Box, which is not formally part of the Signal series but which addresses the same fundamental question: what happens when a signal enters a system that was not designed to receive it, and the system, because it cannot distinguish between the signals it was designed to receive and the signals it was not designed to receive, treats the unexpected signal as a legitimate instruction and acts on it? The Blue Box is a device that produces signals. The telephone network is a system that receives them. The painting is a record of the moment when the device and the system met, and the system, because it trusted the signal, opened. The painting holds that moment still. The tones are not audible. The network is not visible. But the device that produced the tones is present on the canvas, rendered in the specific blue of the original Blue Boxes, and the dark background that surrounds it is the same dark field that Tan Mu uses for all of her technological subjects, the void from which the signal came and into which it disappeared, the switching system that received the tone and opened the line and never knew that the tone had come from a device the size of a cigarette pack held up to a telephone handset by a college student in a dormitory room in Berkeley in the early 1970s. The painting does not celebrate the hack. It records the device. And the device, sitting there on the dark ground, is not a symbol of rebellion or resistance or counterculture. It is a piece of hardware that produced a specific frequency, and the frequency, because it was the right frequency, was enough. The system did not require authorization. It required the tone. The tone was sufficient. The painting is about the sufficiency of the tone.